Discover Zero Trust SD-WAN
SD-WAN connects branches, sites, and data centers in a flexible and advanced way. But today’s networks require Zero Trust controls to secure all communications—even between internal users and applications. Zero Trust SD-WAN brings a new level of control and security to every connection.
Enforce Zero Trust Across Your Internal Networks

Teldat’s SD-WAN secures access to cloud and private data center apps from any location. With built-in ZTNA and a Zero Trust approach, it enforces consistent, granular policies for every user and device—no matter where they connect from. Zero Trust SD-WAN is ideal for managing closed devices:
- Applies Zero Trust principles to SD-WAN environments
- Enforces consistent policies for all users, everywhere
- Isolates users and devices with identity-based segmentation
- Integrates threat prevention across all traffic flows
- Secures IoT devices with Zero Trust access
Zero Trust SD-WAN Access at a Glance
The SD-WAN (Software-Defined Wide Area Network) market is growing rapidly as companies increasingly depend on cloud connectivity and require flexible, secure, and efficient networks.
SD-WAN offers numerous advantages, such as optimizing traffic across multiple WAN links, improving access to key applications, and enabling centralized management. Teldat’s SD-WAN can be deployed in the cloud or on-premise in customer datacenters, and its overlay model simplifies control and configuration by abstracting the underlying infrastructure.
Flexibility is another key benefit—such as the scalability to add new sites in just a few clicks. It also seamlessly supports both traditional MPLS connections and rapidly growing access technologies like FTTH and 5G.
Security is equally critical in SD-WAN networks—integrating advanced traffic protection features is no longer a choice. Integrated protections like firewalls, IDS/IPS, anti-malware, and sandboxing must be implemented to keep threats out. In addition, fine-grained access control is required to ensure users only reach what they’re authorized to—nothing more.

What are the important points related to Zero Trust SD-WAN?
Simple Authentication and Access Control
Supports user access from any location with a hybrid architecture and Active Directory integration. Enables granular access policies for applications and services.
Unified Management Console
Through a single console, Teldat customers apply consistent policies and manage both their SD-WAN network and integrated security features from one centralized interface.

Advanced Monitoring and Detection
Teldat’s be.Safe XDR offers a full dashboard for administrators, showing user activity, access behavior, and communication status—alongside real-time threat detection.

Threat Protection
As cyber threats evolve, Teldat integrates threat prevention and DLP to detect suspicious behavior, known attacks on internal systems, and potential data leaks.
Understanding and Extending Zero Trust to SD-WAN
Combining SD-WAN with Zero Trust strengthens both security and business connectivity. While SD-WAN enhances network performance, Zero Trust removes implicit trust by continuously verifying every user, device, and application before granting access. This ongoing verification reduces the risk of unauthorized access and protects critical applications across distributed environments.
A key pillar of Zero Trust in SD-WAN is the principle of least privilege: users are granted access only to the resources they need. Micro-segmentation divides the network into secure zones, limiting lateral movement and containing threats in the event of a breach. SD-WAN also encrypts traffic with protocols like IPsec, ensuring data is protected in transit and minimizing the risk of malicious interception.
Visibility and continuous monitoring are also essential. Zero Trust SD-WAN leverages advanced tools such as real-time traffic analysis, behavior analytics, and anomaly detection to uncover suspicious activity.
With integrated ZTNA, unified access policies are applied consistently to both internal and remote users. This enables a proactive security approach and supports hybrid and multi-cloud environments—delivering secure, agile, and resilient connectivity in the face of today’s cybersecurity challenges.

Zero Trust SD-WAN Solutions and Teldat Products
Context
Zero Trust SD-WAN is essential for companies looking to strengthen security across distributed networks, minimize risk, and gain better traffic control. SD-WAN improves connectivity between branches offices, data centers, and cloud services, while delivering strong protection against advanced threats.
Zero Trust complements SD-WAN by eliminating implicit trust and reducing the attack surface. In traditional networks, compromising a single point can allow attackers to move laterally without restriction. Zero Trust addresses this with micro-segmentation—restricting access to only the necessary resources and blocking unauthorized movement within the network.
Teldat’s Zero Trust SD-WAN delivers the internal segmentation and advanced security today’s networks demand. With integrated ZTNA for remote users, it enables unified, simplified access policy management across the entire platform. Customers can build their WAN using a secure overlay that interconnects remote sites with data center or cloud services—all within Teldat’s be.Safe and SD-WAN suite.
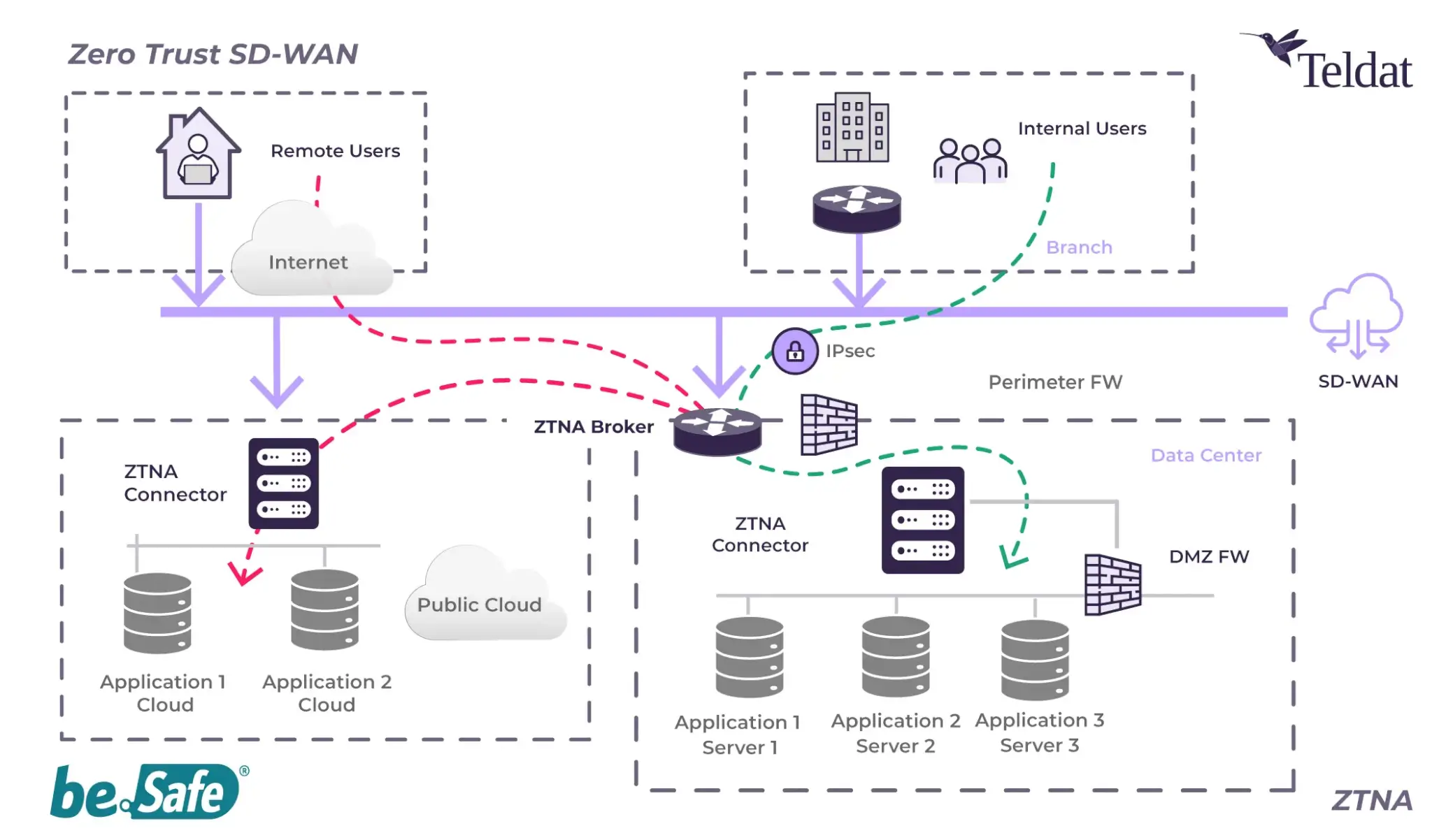
Zero Trust SD-WAN Architecture
Teldat deploys a hybrid architecture built around a Broker, which serves as the central SD-WAN hub. It receives encrypted tunnel connections from branch offices and remote users, and it’s where authentication, device compliance checks, and granular access policies are enforced.
Zero Trust connectors are deployed close to applications—whether in data centers or public cloud environments. Customers can install as many connectors as needed to match their network’s scale. Available as physical or virtual appliances, these connectors run Teldat’s hardened operating system and include built-in threat inspection features.
Remote users connect via an agent installed on their device, while on-site users are authenticated through seamless Active Directory integration. Other endpoints, such as IoT devices, are managed using granular access policies and identified by IP or MAC address, especially when integrated with NAC systems.
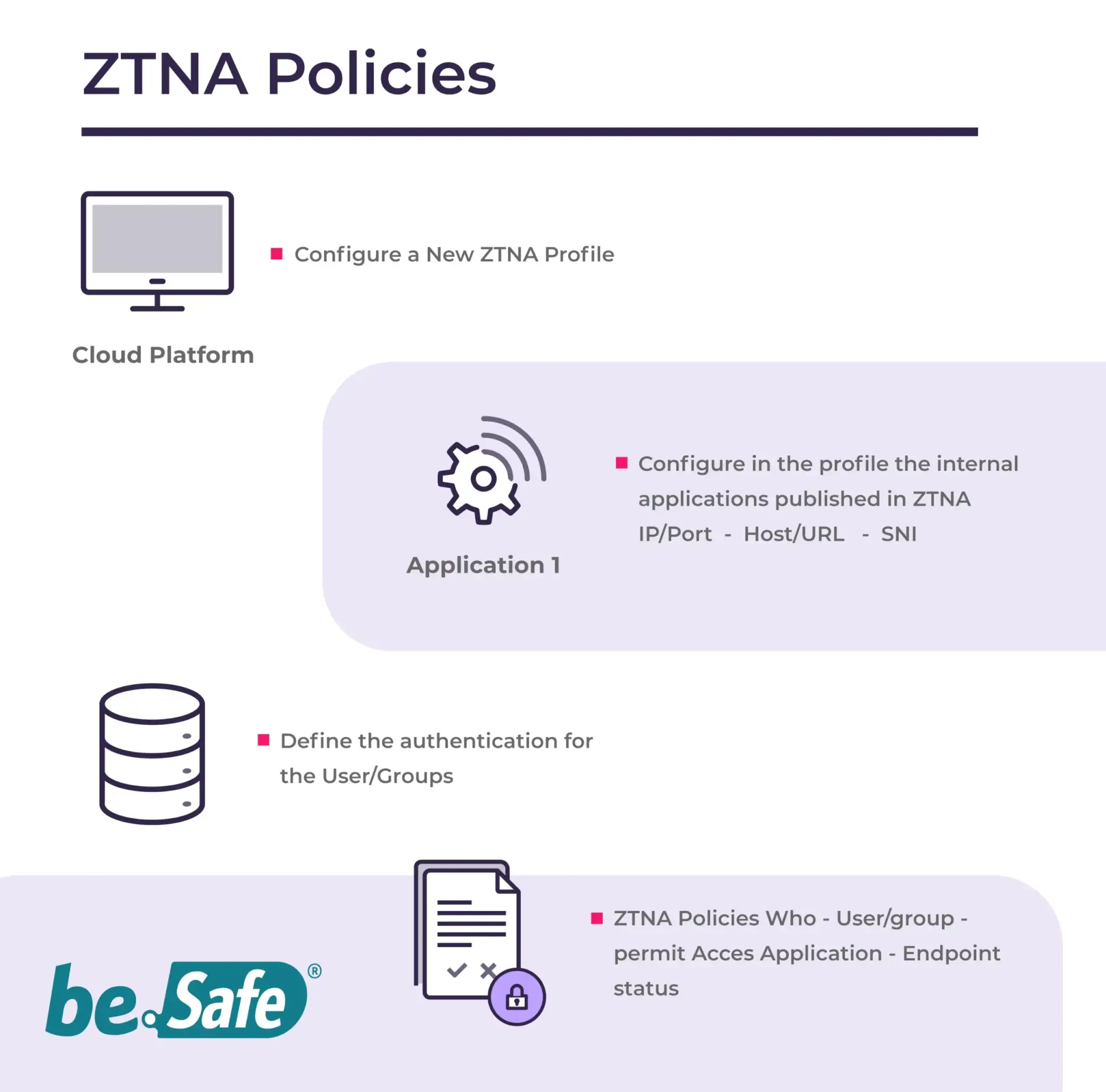
Polities and Advanced Features of Zero Trust SD-WAN
Once the components are deployed and users have the agent installed on their devices, applications can be registered by host, URL, IP address, or port. Combined with directory-based authorizations, this enables the creation of specific, profile-based access policies tailored to each user—regardless of their location.
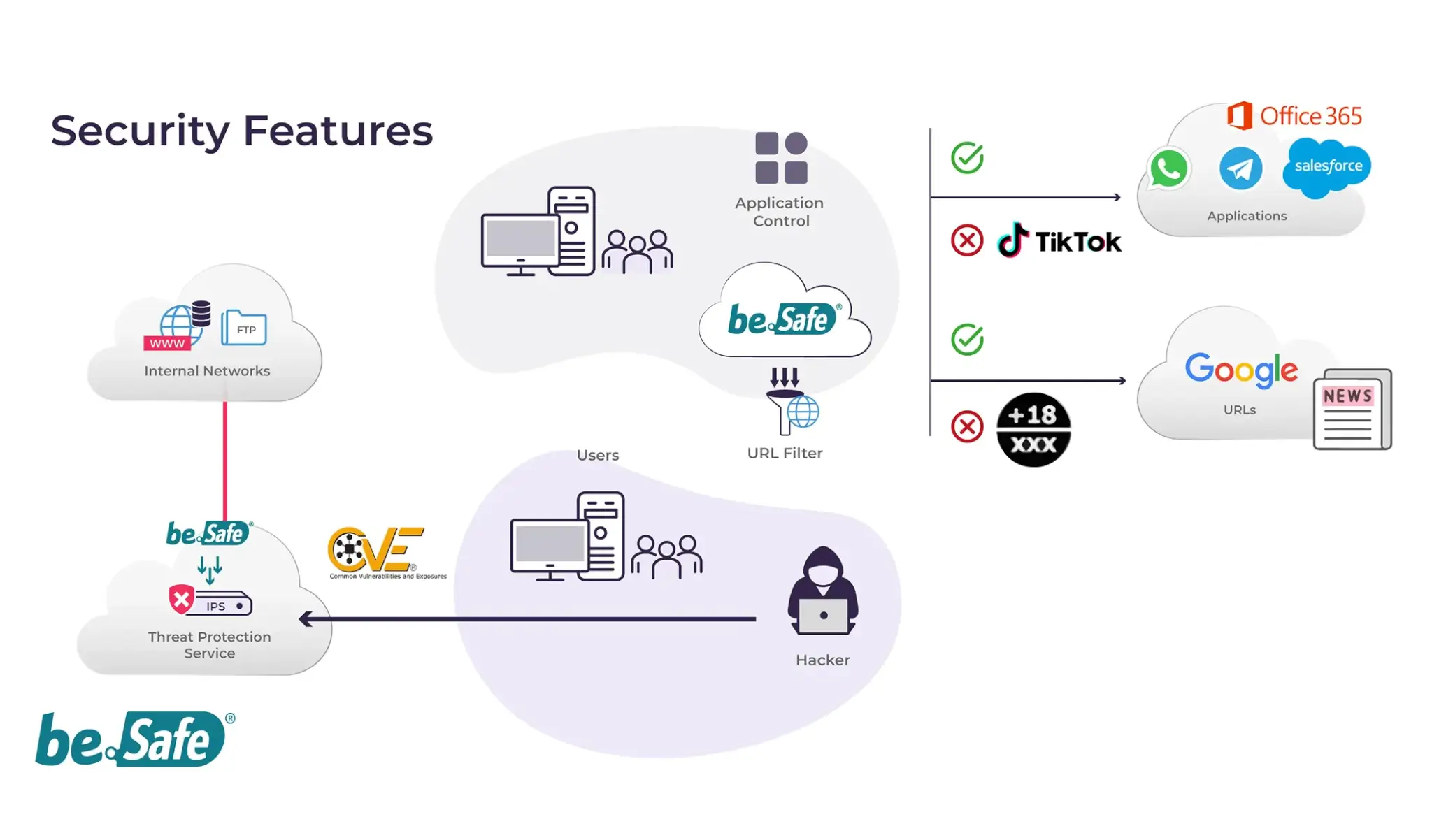
Advanced Security Features
Alongside the be.Safe Pro product suite, Teldat offers a wide range of advanced security capabilities. Administrators can easily apply threat prevention profiles to any traffic flow—whether directed toward internal applications or the Internet—ensuring consistent protection across the entire platform. Additional features include URL filtering and application control.
IoT devices are secured without the need for an installed agent. Since they connect via Teldat’s physical appliances through encrypted tunnels to the SD-WAN service, their origin can be identified and visibility and control policies can still be enforced.
Zero Trust SD-WAN Use Cases
SMBs in SD-WAN Environments
Small and medium-sized businesses are adopting SD-WAN to securely connect users to their applications and services.
Application Control and Visibility
Enforce stricter policies to limit and isolate access from remote ATMs to internal applications—preventing lateral movement across the network.
SMBs in SD-WAN Environments
Small and medium-sized businesses are adopting SD-WAN to securely connect users to their applications and services.
Challenge
SMBs often rely on internal applications hosted on servers located at a single office or shared data center. Many also operate remote branches or stores that require different types of access. SD-WAN provides greater flexibility and reduced connectivity costs—but it also calls for more granular access policies to ensure proper security.
Solution

Teldat’s security solutions allow remote users to connect from branch offices or external locations. With a Zero Trust approach, customized access policies can be applied per user or user group, ensuring each user only receives the permissions they truly need.
This guarantees access confidentiality and full control across the network—aligned with the core principles of Zero Trust.
Why Teldat?
Teldat offers robust, flexible security solutions with intuitive interfaces that make it easy to manage access and connection policies—even for non-technical users. Zero Trust policies can be quickly and easily implemented through Teldat’s Zero Trust SD-WAN.
Financial institution increases control and visibility over application access
Enforce stricter policies to limit and isolate access from remote ATMs to internal applications—preventing lateral movement across the network.
Challenge
This organization uses MPLS connections to link branch offices and remote ATMs but does not apply access permissions based on device type. It also lacks network visibility tools to monitor usage or identify where these devices are connecting.
Solution

Teldat’s security solutions enable granular access control to all corporate applications—whether hosted in data centers or the cloud—through seamless ZTNA integration. Administrators can define which applications are accessible from branches, ATMs, or mobile devices.
With integrated visibility tools, you can monitor who is accessing which resources and from where. This helps detect policy violations or unusual activity from potentially compromised devices and supports ongoing refinement of access policies.
Why Teldat?
Teldat’s Zero Trust SD-WAN and be.Safe XDR solutions combine secure, granular access with customizable dashboards for clear traffic visualization. The platform is hardware-agnostic and supports any device that meets tunneling and flow-reporting standards.
Internal and External User Access
Company looking to seamlessly integrate external and internal user access.
Challenge
Segmenting internal networks to control resource access is already complex—and it becomes even more challenging when remote users and third-party providers are involved. Some users must be restricted from accessing resources outside their department and should only reach what is specifically assigned to them, whether they connect from home or the office. There’s also a risk that a compromised vendor device could trigger a broader breach through lateral movement.
Solution
With SD-WAN and ZTNA solutions, networks can be fully segmented, and access can be controlled based on user or device identity. Administrators can apply consistent traffic policies—across data centers and cloud services—through a single, centralized graphical interface.
Thanks to micro-segmentation, if a device is compromised, the threat is contained within that segment and cannot spread across the wider network or reach central servers.
Why Teldat?
Teldat’s Zero Trust SD-WAN and ZTNA solutions offer secure, segmented access with intuitive interfaces and centralized policy management. Advanced security features are easy to deploy, helping ensure users and devices are isolated and can only access what they’re authorized to—regardless of where they connect from.
Read our latest Blog Post
Why industrial OT security specialization is no longer optional
The factory floor is now a cyber battlefield. As industrial environments become increasingly connected, the traditional approach of treating Operational Technology (OT) security as an afterthought—or worse, as an extension of IT security—is proving dangerously...
What is the CCN and how does it relate to the ENS, the CPSTIC Catalog, and cybersecurity products?
In Spain, public-sector cybersecurity is structured around several key concepts: the National Cryptology Center (CCN), the National Security Framework (ENS), the CPSTIC Catalog, and the Qualified and Approved cybersecurity products listed within it. Although closely...
From Firewalls to XDR: A Historical Journey Through Enterprise Cybersecurity
The Ever-Evolving Cyber Threat Landscape Over the past few decades, cybersecurity has undergone a profound transformation in response to an increasingly interconnected and digitalized world. What once revolved around basic perimeter defenses—such as traditional...